A Guide to Third Party Risk Management
 Organizations today rely on third party vendors, applications, and services to meet their objectives and requirements. While there are benefits to partnering with third parties to achieve these objectives, it also introduces a new element of risk that must be reviewed and managed. Understanding and mitigating third party risk has become more important than ever, which makes now the perfect time for your organization to implement a third-party risk management program.
Organizations today rely on third party vendors, applications, and services to meet their objectives and requirements. While there are benefits to partnering with third parties to achieve these objectives, it also introduces a new element of risk that must be reviewed and managed. Understanding and mitigating third party risk has become more important than ever, which makes now the perfect time for your organization to implement a third-party risk management program.
Third parties pose a persistent risk as they are often holding data on behalf of the organization. If you use a third party that handles your data, you are still responsible for anything that happens to that data, making third-party risk management crucial in reducing the likelihood and impact of data breaches, operational failures, and reputational damage. Typical third-party risks include events such as a data breach or denial of service for an outsourced process. Third-Party Risk Management is the process of analyzing and mitigating these risks to your organization.
This guide covers several aspects of third-party risk management:
- Developing a third-party risk management program
- What if my third party doesn’t have a SOC 2 Type 2 or other Cybersecurity Certification?
- GRF’s open-source scanning technology in third party monitoring
- Where are we seeing new risks?
- Simple Next Steps
- GRF Can Help
Developing a third-party risk management program
Third parties can include vendors, suppliers, partners, contractors, or anyone who has access to internal organizational data and/or your network. Since they have access to your information, you need to understand exactly how these third parties are operating. There are 5 key steps to developing, implementing, and maintaining a third-party risk management program.
1. Determine and create a risk management framework for third parties
As with all frameworks, it should outline the objectives, roles, responsibilities, and governance of the program. Just like a traditional risk management program, it will identify the organization’s risk appetite (acceptable level of risk), risk tolerance (how much risk is acceptable), risk mitigation strategies (accept, avoid, mitigate, transfer), and risk treatment plans. The assessment of risk should align with the organization’s core objectives to help identify which third parties are more critical than others, and which ones introduce greater levels of risk.
2. Identify and evaluate your current third parties
- Identify all the third parties that your organization uses. Typically, these third parties will have access to your systems or data. Examples include your accounting system, CRM, email system, file sharing platform, etc.
- Verify what data or function that third party holds for the organization.
- Rank these third parties based on criticality. For example, tier 1 criticality typically holds critical organization information, is crucial to the day-to-day activities, and would cause significant issues if they had a breach or if the service was unavailable. Additionally, any third party that is holding personally identifiable information (PII) would be deemed as a tier 1 criticality as the loss or exposure of PII could lead to fines, reputational issues, and a loss of trust ultimately affecting both the individuals who trusted you with their data and your organization as a whole.
- Document the evaluation. Organize your third parties by rank (can use a criticality scale such as 1-3) and include documentation of what processes each entity performs and the types of data they access. This evaluation will help to identify the top risks that your current third parties pose to your organization. This documentation also makes it easier for your risk management team to track and manage these relationships and risks.
3. Introduce/Implement a due diligence and vetting process (Risk Assessment for third parties)
When looking at implementing new third-party solutions, you should always perform a vetting process. This will ensure that you have done your due diligence before signing a contract with the third party. This third-party risk checklist can be used as a starting point for creating these questions. You can also track answers within your platform or spreadsheet. Items to consider include:
- Are they solvent?
- Do they follow any information security standards or frameworks? Are they certified? For example, SOC 2 type 2 or ISO 27001.
- Do they outsource any of their services?
- Have they experienced a cybersecurity incident?
- Are formal information security policies and procedures implemented?
- Are employees required to complete security awareness training?
- Do they have data recovery capabilities such as offsite backups?
- Are there Data Loss Protection (DLP) solutions in place to prevent the exfiltration of sensitive data?
- Are there ongoing vulnerability tests internally and externally facing?
- Is there a formal patching policy in place?
4. Establish Risk Owners and Treatment Plans for Third Parties
- Define who in your organization is responsible for the review of the third party and relationship. That person will be responsible for managing the risks that the third party introduces to the organization.
- Once third-party risks are identified, the owners should develop risk treatment plans. For example, if the risk is that an unauthorized user could access your third-party accounting system, then a treatment plan may be to require your users to create a complex password along with MFA (multi-factor authentication) when using this application. Additionally, you can require the user to not use the same password for this site as their network password.
- The identification in step 2 and the responses to questions in step 3 above will help to identify those top risks from third parties.
5. Continuously monitor and review the program/third parties
- Implement a continuous monitoring solution to regularly review third parties.
By using the tiered criticality rankings, you can develop a process for how often and how intensive the reviews of the third parties would be. For example, a tier 1 criticality third party may be continuously monitored and reviewed monthly to determine if there are any security concerns around their activity. However, a lower criticality/risk third party may only need to be reviewed annually to ensure they are continuing to implement security best practices and maintaining their compliance with regulations and standards. - Review the identified risks regularly, but perform an annual review to identify any new third parties or third parties that are not up to par with the organizational requirements.
- You can utilize software such as our cyber scorecard to track third parties.
- The Kaseya Ransomware Attack is a stark example of the consequences of not monitoring third parties to identify potential weaknesses.
What if my third party doesn’t have a SOC 2 Type 2 or other Cybersecurity Certification?
SOC reports are issued by independent auditors and provide valuable information about a vendor’s internal controls, security measures, and overall risk management processes. Your critical third-party vendors may not have a SOC 2 Type 2 certification for their security and control practices, but the absence of a SOC report doesn’t necessarily mean that the vendor is untrustworthy or lacks security measures. It might simply indicate that they haven’t undergone a formal SOC audit or chosen not to disclose the report publicly. To cover this possibility, include criteria for evaluating and managing third-party risks in your vendor risk management policy. This policy should guide your decisions when dealing with vendors without SOC reports. Below are ideas to give your organization some peace of mind.
- Request Internal Documentation:
Ask the vendor for any internal documentation related to their security controls, policies, and risk management practices. This could include security policies, incident response plans, access control procedures, and other relevant documents. - Conduct a Security Questionnaire:
Create a detailed security questionnaire that covers various aspects of their security practices and risk management. Request the vendor to fill it out and provide specific details about how they address security concerns. - Seek an Independent Security Assessment:
Consider conducting an independent security assessment of the vendor’s software and infrastructure. You can hire a third-party security firm to perform penetration testing, vulnerability assessments, or a security audit. - Check Customer References:
Speak with other customers who have used the vendor’s software. Ask about their experiences, any security incidents they might have encountered, and how the vendor handled such situations. - Add Contractual Protections:
Establish clear contractual terms regarding security requirements, data protection, and liability in the event of a security breach. Include provisions that mandate the vendor to notify you promptly of any security incidents or changes to their security practices. - Perform Continuous Monitoring:
Once you decide to engage with the vendor, implement continuous monitoring and periodic assessments to ensure they maintain appropriate security practices throughout the duration of your relationship. Tools such our continuous auditing can help to provide insight into your critical vendors.
GRF’s open-source scanning technology in third party monitoring
To address risks like data breaches, operational failures, or reputational damages, GRF’s open-source scanning technologies can help you assess and provide feedback to third parties and partners on how to improve their cyber posture. This shows your organization’s commitment to security and privacy. Open-source threat scanning can provide insight and analysis into various areas.
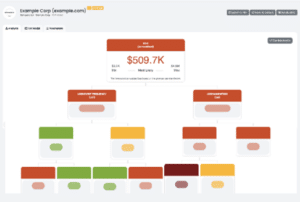
Technical Risk Assessment
Our cybersecurity scorecard identifies and scores key security areas where your third party is strong or is falling short. The assessment looks at 20 different categories and provide an overall risk score based on potential technical vulnerabilities. This report enables you to track scores over time and better understand the level of exposure presented by the third party.
- Potential financial loss
Quantifying the financial risk a third party may pose to your organization helps to bring awareness to the importance of monitoring and managing third parties. By evaluating the loss event frequency (how often something may occur) and the loss magnitude (amount impacted), you can quantify the overall risk the third party poses.
- Compliance and Regulatory Requirements
Requiring third parties to adhere to compliance requirements reduces the risk of a data breach and the potential recovery costs from them. Through our technology, you can measure the compliance level of any company compared to several regulations and standards. Our technology will parse the third-party site and provided policies/procedures and compare them to regulations and standards such as NIST CSF, ISO 27001, GDPR and others.
- Vendor Selection
You can use Open-source scanning results during the vendor selection process. The results will help to identify the third parties that are committed to cybersecurity and privacy.
- Transparency and Accountability
By performing an open-source scan, you can share the results with the third parties to hold them accountable during the monitoring process. This allows you to understand what their processes are for managing potential vulnerabilities and how they secure their application over time.
Where are we seeing new risks?
AI tools such as ChatGPT have exploded onto the scene and organizations have increased their usage of them. Since AI tools are typically provided by an outside source, they qualify as a third party and can represent additional risks to your organization. If your organization uses AI, you should start identifying all the tools your organization uses and creating policies around them.
AI usage should follow your organization’s security policies. Things to consider including within the policy include:
-
-
- Evaluation of IT tools
Your IT team should evaluate the third-party tool to ensure it complies with internal security policies. - Protection of Data
There should be guidance on the information you can and cannot share with the tool. The general rule of thumb is to not share any internal, confidential, or donor/client data with it such as email addresses, donation amounts, phone numbers, PII, etc. - Access controls
The password to the AI system should never be the same as your network password in case the AI tool has a breach of their held usernames and passwords.
- Right to audit
Track all AI tools used so you can monitor their use. For example, you can review activity from a randomly-selected user to see what information they are sharing on the tool. This will ensure that you can check use of the tools regularly.
- Evaluation of IT tools
-
Just as the pandemic brought an increase in cloud service providers for organizations, the increase in AI tools may have a similar effect. It is just as important to understand the risks associated with them as a third party.
Simple Next Steps
-
-
- Assess your baseline: What are our goals, and critical functions and what can we implement to support this (ex. risk management framework to follow)?
- Catalog all third parties: Catalogue your third parties and perform a risk review to identify potential top risks from them.
- Assess Risks: Rank your third parties based on criticality and assess the risks that they present.
- Conduct Vetting and Due Diligence: Implement a process for evaluating new and current third parties.
- Identify owners of third parties: Determine who is responsible for the review of third parties and the risk treatment plans for the third party.
- Monitor and Review: Monitor your third parties regularly and review the plan/process at least annually.
- Plan for the future: New technology and organizational needs will cause your risks and key process to change over time, so your third-party risk program will need to as well.
-
GRF Can Help
A GRF, we have the tools, knowledge, and experience to help support your organization in developing a robust third-party risk management policy and program so that your third-party risk is adequately addressed. Please contact us to get started today, or reach out to us at the contact info below.


 Technical Risk Assessment
Technical Risk Assessment