October 4, 2021
GRF Cybersecurity Risk Assessment and Scorecard Blog Series
Most organizations have secured their data with encryption, but security protocols are evolving rapidly in response to sophisticated cyberattacks. Ensuring your organization has the latest SSL/TLS protocols enabled is necessary to help establish trust, ensure data privacy for your users, and to prevent data breaches.
Risks of Man in the Middle Attack (MitM)
If the data on your servers is not encrypted before transmission, attackers can steal information without having to hack into your system. They just need to find a way to intercept the flow of information from the server to a trusted device.
One way is called a “Man in the Middle” attack. The attacker will intercept the data exchange happening between a client device and the server using software. From there, the attacker can copy or modify the data and send it on to the server so that the server does not detect a breach. The server then will respond to the MitM software as if nothing is wrong. The software in the middle may be stealing credentials, modifying information, or collecting the information for unauthorized use which breaches the integrity and confidentiality of the data. Neither the end-user nor the server is aware that a breach has happened.
What is SSL/TLS?
Secure Socket Layer (SSL) is the original protocol that encrypts information that travels across the internet. As vulnerabilities were found in SSL, a new protocol took its place, Transport Layer Security (TLS). TLS evolved from SSL and provides privacy and data security when communicating over the internet. When you input a password or credit card information into a website with encryption, that data is not able to be seen by hackers or eavesdroppers, thus ensuring privacy for your data.
In a report from the NSA, “Eliminating Obsolete Transport Layer Security (TLS) Protocol Configuration”, they recommend that only TLS 1.2 and 1.3 be enabled, while other less secure, legacy encryption methods should be disabled.. Many organizations have TLS 1.2/1.3 enabled and believe that they are safe and secure. However, its predecessor, TLS 1.0/1.1 may still be active, which provides a way for hackers to take advantage of the outdated protocols. For example, Google Chrome is updated to only allow users to use the most up to date protocol associated with the web browser, however, if an attacker utilizes an older browser, they can still access the website from the older TLS protocol which would leave your organization vulnerable to sniffing attacks.
SSL Certificates
To enable trust in your website from users, your organization must have an SSL certificate. An SSL certificate provides data security, prevents users from creating a fake website, and provides trust from the users when relaying data to your website. To determine whether your website has an SSL certificate attached to it, you can look in the left side browser and see if your website has a lock next to the address window. If it has the lock, then you have a valid certificate attached and shows as trustworthy to users.
As data protection has become more and more important, web browsers have begun to label websites as not secure when there is not a valid SSL certificate. It can affect a user’s trust in your website. It can also reduce traffic to your website, because Search Engine Optimization (SEO) is impacted by whether your website can be trusted. If there will be any information transmitted from a user to your website such as passwords or credit card information, then you must have TLS 1.2/1.3 enabled.
How GRF Can Help
Our experts can conduct a review and generate a SSL/TLS strength report, which provides you with an assessment of available cipher suites, known SSL/TLS vulnerabilities, server misconfiguration, invalid SSL certificates, and more.
The assessment will:
- Verify that an SSL certificate is valid and trusted
- Inspect server configuration
- Provide a score based on the categories being evaluated
- Provide vulnerability checks
We will identify any vulnerabilities that may be facing your organization. Since our scan looks at open-source threat intelligence, this is information that a hacker would be able to utilize to expose your organization. The report will provide remediation steps to help secure your data and prevent against man in the middle attacks, a lack of trust, and identify out of date certificates.
Trust in your online presence is critical in gaining support for your organization. As part of our cybersecurity audits, our Cybersecurity Risk Assessment and Scorecard can identify, remediate, and protect your organizational assets.
For more information on GRF’s Cybersecurity Risk Assessment and Scorecard, or about our cybersecurity capabilities, reach out to our IT & Risk Supervisor Darren Hulem, CISA, Security +, or Risk Analyst Tom Brown, CAPM, through our contact us page.
For more on MitM attacks, read the online article from CSO.
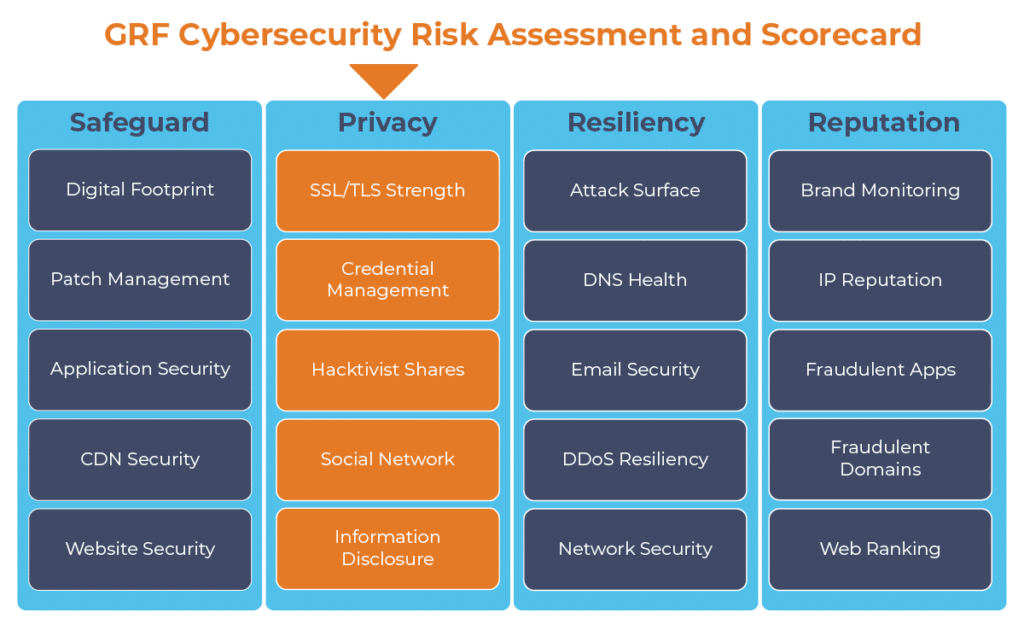
The digital transformation happening in the workplace requires heightened awareness of your organization’s cybersecurity posture. Managing the risks has become another full-time job. The GRF Cybersecurity Risk Assessment and Scorecard helps identify possible weaknesses and vulnerabilities by evaluating risk in 20 different categories. The scorecard will evaluate your cyber posture, propose remediation steps, and help eliminate vulnerabilities that your organization is facing.