April 14, 2023
 Developing and maintaining a third party risk management (TPRM) program can help to reduce the overall risk to your organization.
Developing and maintaining a third party risk management (TPRM) program can help to reduce the overall risk to your organization.
What is TPRM? In short, it is the process of analyzing and mitigating risks associated with working relationships with outside entities. These parties can include everyone from contractors providing janitorial services to suppliers of a critical component to your manufacturing process. Risks to third-parties are also risks to your organization. A plan for managing third-party risk protects your organization from unsuspected threats and nasty surprises (read more about TPRM in our article here).
Evaluating third parties can be done in multiple ways, but we have found it essential to conduct evaluations in three stages: during the vetting process, during ongoing monitoring, and during annual reviews.
- Vetting – When contracting for a third party, especially one that will be holding sensitive or confidential data, it is critical that you have gone through and asked them questions relating to their security practices, policies, and procedures. Since they will be holding your data and potentially donor, customer, and employee data, you need to ensure they are set up to protect that information.
- Ongoing Monitoring – Once you have selected a third party to use, it is important to continue tracking what data is shared with them and determine if they are upholding their contract requirements. For example, if a third party is managing your website, are they keeping up to date with patches or application security items? This should be discussed regularly and reviewed on an ongoing basis.
- Annual Review – At least on an annual basis, your organization should take an inventory of all the third party applications, vendors, contractors, etc. that have been used within the year and determine their applicability to the organization. Did you use them as you expected to? Did they have any security issues or breaches? Were they easy to communicate with? Having an annual questionnaire and re-vetting process can help to alleviate concerns you may have when managing third parties.
Making sure that the data you share with third parties is secure is critical, as your organization can be liable in the event of a breach.
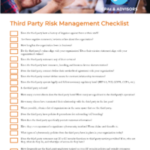
Managing third parties is no easy task, so we have developed a risk questionnaire checklist that can help provide a framework for asking questions about their security, which you can view here.
We Can Help
If you need assistance in creating a third party risk management program, or reviewing your existing program, we can help! Contact us online, or at the information below.